Hidden features in software used to feel like inside jokes between developers and curious users. But in 2026, that same hidden code can trigger a security audit warning.
A software egg—often called a software Easter egg—is still a fascinating part of software culture. From secret mini-games to hidden messages, these features reflect creativity inside code. Yet today, they exist in tension with modern security standards, automated testing pipelines, and AI-assisted development.
This guide goes beyond the basics. It explains what a software egg is, how it works, and—more importantly—how it fits into modern CI/CD pipelines, security frameworks, and AI-driven development workflows.
What Is Software Egg?
A software egg is a hidden feature, message, or behavior intentionally embedded in software, typically not documented and only triggered under specific conditions.
In simple terms, it’s a deliberate secret inside the codebase.
Unlike bugs, these are intentional. Unlike standard features, they are hidden.
You’ll typically see software eggs as:
- Hidden UI interactions or animations
- Secret commands or input sequences
- Embedded mini-games
- Developer credits or messages
A classic example is the 1979 Atari Adventure Easter egg, where developer Warren Robinett hid his name—widely considered the first known instance.
Semantic context (important for search engines)
Software eggs are closely related to:
- Software Easter eggs
- Hidden features in applications
- Easter egg programming
- Secret developer features
- Debug shortcuts and hidden commands
- Undocumented code paths
How Software Egg Works
At a technical level, a software egg is simply conditional logic that is intentionally obscured.
Step-by-step breakdown
Hidden Code Path
Developers write logic that is not part of the visible UI or documented features.
Trigger Mechanism
The code is tied to a specific condition, such as:
Key sequences (e.g., Konami Code)
URL parameters
Repeated UI interactions
Special input strings
Execution Layer
When triggered, the system executes the hidden function.
Isolation (Ideally)
Well-designed eggs are isolated so they don’t interfere with production logic.
Example (simplified JavaScript trigger)
| // Store the keys the user presses
let userInput = []; // The secret code we want to detect const secretCode = “uuddlrlrba”; // Listen for every key press document.addEventListener(“keydown”, function (event) { // Add the pressed key to our list userInput.push(event.key); // Convert the array into a string const inputString = userInput.join(“”); // Check if the secret code exists in the input if (inputString.includes(secretCode)) { console.log(“Easter Egg Activated!”); }}); |
How it works (simple explanation)
- Every time a key is pressed, it gets saved in
userInput - We turn that list into a string (
"uuddlrlrba"style) - Then we check: does this string contain our secret code?
- If yes → Easter egg triggers
This kind of implementation is simple—but in modern systems, it’s rarely left undocumented.
How Software Eggs Fit Into Modern Development (2026 Reality)
This is where things get interesting—and more serious.
In modern pipelines, hidden code is no longer just “fun.”
In CI/CD environments:
- Automated tests scan for unused or unreachable code
- Static analysis tools (SAST) flag hidden logic
- Security tools treat undocumented features as potential vulnerabilities
According to modern practices:
Software eggs can be interpreted as:
- Shadow code (code not tracked in requirements)
- Potential backdoors
- Audit risks in enterprise environments
Why teams are more cautious now
- Compliance standards (SOC 2, ISO 27001) require transparency
- Security frameworks like OWASP guidelines discourage hidden logic
- Code reviews prioritize traceability and documentation
In short: what was once clever is now sometimes considered risky.
Types of Software Eggs (Modern Perspective)
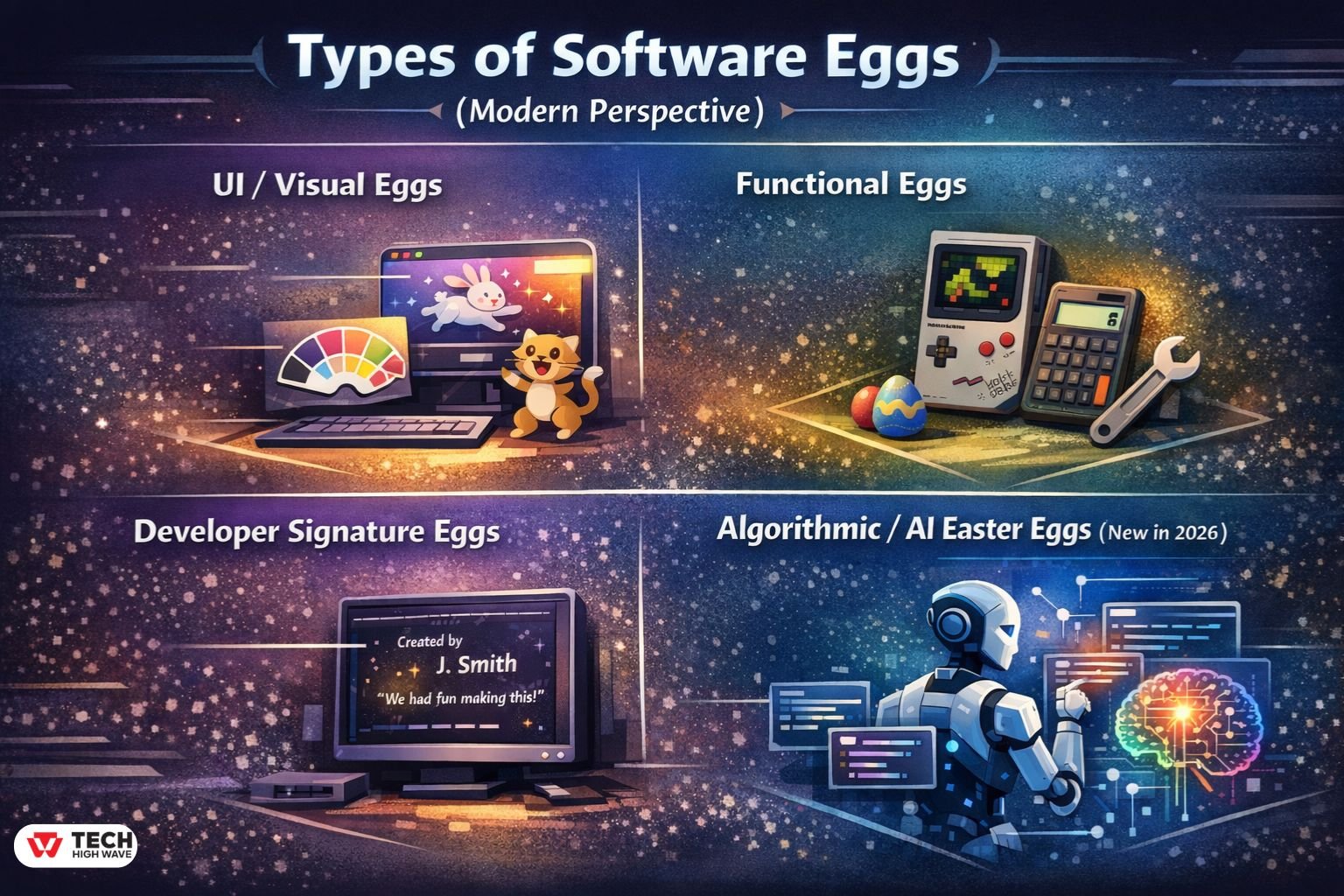
You’ll generally run into four “flavors” of software eggs:
-
UI/Visual Eggs
These are the most harmless—and still common.
- Hidden animations
- Theme changes
- Fun visual responses
Usually safe and widely accepted.
-
Functional Eggs
These include hidden tools or mini-features.
- Built-in games
- Hidden utilities
These can become problematic if undocumented.
-
Developer Signature Eggs
A throwback to earlier software culture.
- Hidden credits
- Personal messages
Rare in enterprise software today.
-
Algorithmic / AI Easter Eggs (New in 2026)
This is the newest category—and the most overlooked.
Instead of UI triggers, these exist inside:
- LLM system prompts
- AI agent behavior rules
- Hidden response triggers
Example:
An AI chatbot might respond differently when it detects a specific phrase—something not visible in the UI but embedded in prompt logic.
These are sometimes called “prompt-layer Easter eggs.”
Real-World Examples (Classic + Modern)
Classic examples
- Atari Adventure hidden room (1979)
- Excel 95 “Hall of Tortured Souls”
- Excel 97 Flight Simulator
- Google search tricks like “Do a barrel roll”
Modern SaaS-style examples (2025–2026 trend)
- Hidden animations in productivity tools
- Slack-style playful responses to certain commands
- Subtle UI surprises in design platforms
These are more subtle—less about secrets, more about delightful UX moments.
Security & Compliance Risks (Critical in 2026)
This is where most modern discussions focus.
Why software eggs are flagged today
Security tools often detect them as:
- Unreachable code paths
- Unauthorized logic branches
- Hidden execution triggers
Common risks
- Introduces unintended vulnerabilities
- Bypasses authentication flows (in worst cases)
- Confuses audit trails
- Creates maintenance issues
How to safely include a software egg
If a team still wants one:
- Document it internally
- Include it in threat models
- Ensure it passes static analysis
- Restrict access (feature flags, dev-only modes)
The rule: If it exists, it must be explainable.
Software Egg vs Shadow Code vs Debug Mode
| Type | Purpose | Risk Level | Visibility |
| Software Egg | Fun / creativity | Medium | Hidden |
| Shadow Code | Untracked logic | High | Hidden |
| Debug Mode | Testing | Low | Controlled |
How to Create a Software Egg (Modern Approach)
Creating one in 2026 requires more discipline than before.
Step-by-step process
- Define intent (fun, testing, branding)
- Choose a safe trigger (non-sensitive input)
- Isolate logic from core systems
- Document internally
- Validate through CI/CD checks
Best practices
- Keep it lightweight and harmless
- Avoid access to sensitive systems
- Use feature flags where possible
- Ensure audit visibility
Common Mistakes Developers Still Make
Even experienced teams slip up.
Watch out for:
- Leaving hidden code undocumented
- Embedding logic in critical paths
- Ignoring security scans
- Mixing Easter eggs with production logic
- Assuming “no one will find it”
In reality, automated tools will find it.
AI-Assisted Development & “Accidental Easter Eggs”
A new risk in 2026 comes from AI coding tools.
Tools like AI copilots can:
- Suggest hidden behaviors unintentionally
- Reproduce patterns from training data
- Insert “fun” logic that resembles Easter eggs
The problem
Developers may not even realize:
- Why the code exists
- What triggers it
- Whether it’s safe
This creates unintentional software eggs, which are far riskier than intentional ones.
Pros and Cons of Software Eggs
Advantages
- Adds personality to software
- Creates memorable user experiences
- Encourages exploration
- Builds developer culture
Drawbacks
- Raises security concerns
- Complicates audits
- Can introduce hidden bugs
- Less acceptable in enterprise environments
FAQs
Q1: What is a software egg?
A software egg is a hidden feature or message intentionally embedded in software, triggered by specific actions or conditions.
Q2: Are software Easter eggs allowed in enterprise software?
They are generally discouraged because security frameworks require all code paths to be documented and auditable.
Q3: What was the first software Easter egg?
The first widely recognized example is in Atari Adventure (1979), where the developer secretly included their name.
Q4: Why are software eggs considered risky today?
They are flagged by security tools as hidden or undocumented logic, which can resemble vulnerabilities or backdoors.
Q5: Can AI tools create software eggs accidentally?
Yes, AI-assisted coding tools can introduce unintended hidden logic based on training patterns.
Q6: How can developers safely add a software egg?
By documenting it, isolating the logic, passing security checks, and ensuring it doesn’t affect core functionality.
Q7: What is an algorithmic Easter egg?
It is a hidden behavior embedded in AI systems or prompts that triggers specific responses under certain conditions.
Conclusion
A software egg started as a creative signature inside code. Today, it sits at the intersection of creativity and compliance.
In modern development, the question isn’t just “Is this fun?”—it’s “Is this safe, documented, and auditable?”
Used thoughtfully, software eggs still have a place. But in 2026, they must evolve from hidden surprises into controlled, intentional design choices.
For More Visit: TechHighWave